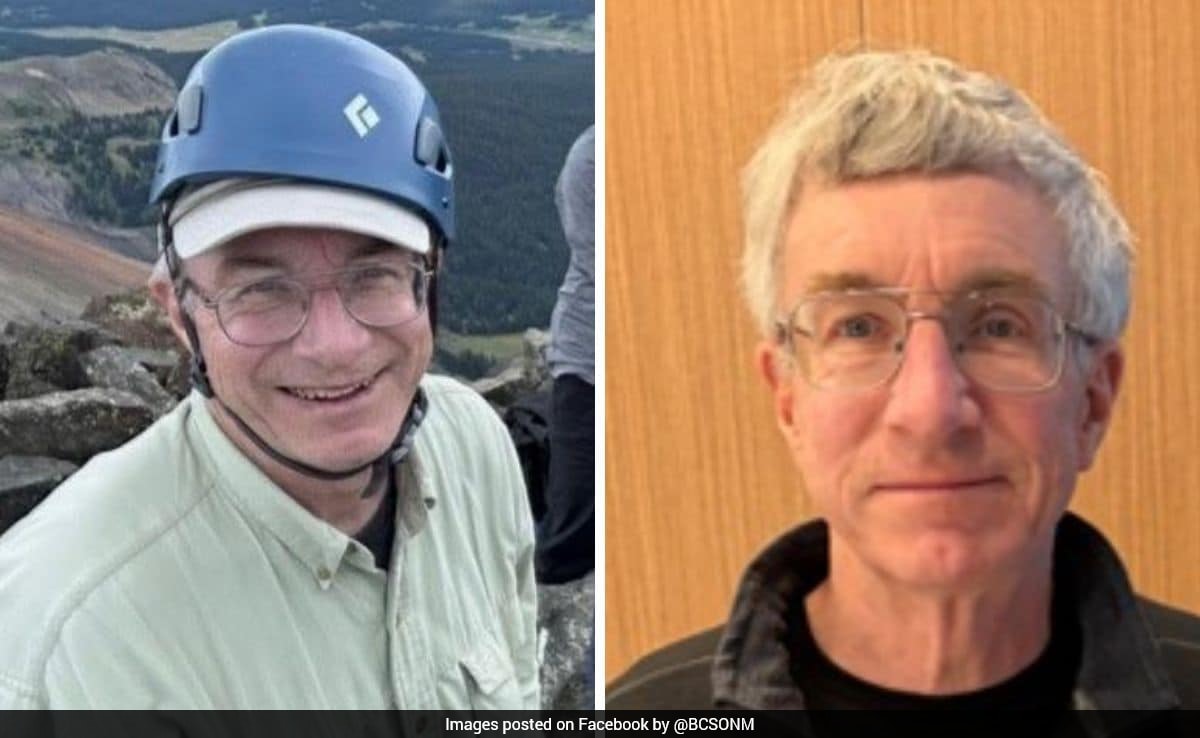
The disappearance of Mark Ruppert, a former U.S. government official with documented access to sensitive Unidentified Anomalous Phenomena (UAP) data, represents a systemic failure in high-value asset protection and intelligence continuity. While public discourse focuses on the emotional narrative provided by his spouse, a rigorous analysis reveals a pattern of behavior consistent with intentional evasion rather than random misfortune. The disappearance operates as a case study in the intersection of classified information exposure, psychological stressors, and the mechanics of "going dark" within a modern surveillance state.
The Logic of Intentional Evasion
When an individual with specialized knowledge of non-standard aerospace platforms or classified defense programs vanishes, the operational profile usually falls into one of three categories: involuntary extraction, accidental expiration, or calculated disappearance. The statements made by Ruppert’s wife—specifically that he "planned not to be found"—shift the probability toward a self-initiated exit strategy. Also making news lately: Finland Is Not Keeping Calm And The West Is Misreading The Silence.
This strategic choice implies a sophisticated understanding of contemporary tracking vectors. To successfully vanish in a digitized society, a subject must solve for three primary variables:
- Financial De-linking: The cessation of all traceable electronic transactions and the conversion of assets into untraceable liquid forms (physical cash or decentralized, unhosted digital assets).
- Digital Ghosting: The permanent abandonment of all hardware associated with a known IMEI or MAC address, coupled with the avoidance of facial recognition clusters in urban hubs.
- The Information Vacuum: The removal of personal motivation from the public record to prevent predictive profiling by law enforcement or intelligence agencies.
Ruppert’s background in high-level government functions likely provided him with the "threat modeling" mindset necessary to execute these steps. The claim that he intended to stay lost suggests a pre-meditated teardown of his personal infrastructure. Further information regarding the matter are explored by TIME.
Categorizing the UAP Knowledge Factor
The correlation between Ruppert’s disappearance and his proximity to UAP data cannot be treated as incidental. In the context of national security, knowledge of UAPs is not merely a collection of anecdotes; it is a high-stakes data set involving advanced propulsion, signature management, and materials science. We must analyze the "Knowledge Burden" through two distinct lenses:
The Intelligence Risk Matrix
If Ruppert possessed actionable data on compartmentalized programs (SAPs), his disappearance triggers an automatic security breach protocol. The risk is quantified by the shelf-life of the information he holds. If the data is operational (active technology), the risk is acute. If the data is historical (past sightings), the risk is reputational.
The Psychological Attrition Hypothesis
The "Whistleblower Stress Cycle" is a recognized phenomenon in the intelligence community. Individuals exposed to information that contradicts the public reality—often referred to as "ontological shock"—face unique psychological pressures. The cognitive dissonance of maintaining a security clearance while processing anomalous data creates a mental bottleneck. If Ruppert felt the disclosure process was stalled or that he was under surveillance, the decision to exit his life becomes a rational, albeit extreme, response to an untenable environment.
The Infrastructure of Disappearance
Ruppert’s transition from a known entity to a missing person requires the exploitation of gaps in the "Total Information Awareness" model. Public reports indicate he left behind items that would typically be essential for a long-term journey. This is a classic tactical diversion.
By leaving behind a phone or a vehicle, a subject provides searchers with a "Last Known Point" (LKP) that is intentionally stagnant. This forces search assets to concentrate on a specific radius while the subject utilizes a secondary, unmonitored transport method to exit the search zone. The efficiency of this maneuver depends on the "Response Lag"—the time between the subject’s departure and the official commencement of the search.
The Cost Function of Persistent Evasion
Maintaining a disappeared state is not a static achievement; it is a continuous expenditure of resources. The subject must constantly solve for:
- Base of Operations: Securing shelter without providing government-issued identification.
- Logistics: Obtaining food and medicine without entering monitored supply chains.
- Social Isolation: The total cessation of communication with a known support network, which is the point where most intentional disappearances fail.
Ruppert’s spouse’s commentary serves as a critical data point here. By publicly stating he did not want to be found, she inadvertently reduces the pressure on state resources to conduct a rescue operation, potentially providing Ruppert with the "clearance" he needs to establish his new identity without active pursuit.
Structural Failures in Oversight and Protection
The disappearance exposes a broader vulnerability in how the U.S. government manages personnel with "Anomalous Knowledge." Unlike traditional nuclear or cyber secrets, UAP information is currently in a state of legislative flux.
The second limitation of current protocols is the lack of a "Safe Harbor" for officials experiencing psychological distress due to classified exposure. When an official feels they cannot discuss their reality with their family, their peers, or a therapist due to Non-Disclosure Agreements (NDAs), the system creates a pressure cooker effect.
This creates a bottleneck where the only perceived options are total silence or total flight. Ruppert’s disappearance may be the first visible data point in a trend of "knowledge leakage" where experts opt-out of the system entirely rather than navigating the friction of the declassification process.
The Mechanism of "Planned Not To Be Found"
To analyze the phrase "planned not to be found" through a strategic lens, we must look at the specific methods used to defeat modern search and rescue (SAR) algorithms. SAR operations rely on "Probability of Area" (POA) and "Probability of Detection" (POD).
$$POA \times POD = POS (Probability of Success)$$
If a subject intentionally manipulates the POA by providing false leads or using terrain that masks heat signatures (thermal IR), they drive the POS toward zero. An official with knowledge of high-end sensor arrays—the kind used to track UAPs—would be uniquely qualified to understand the limitations of the sensors used by local search parties. This is not a man lost in the woods; this is a man navigating the "blind spots" of a technological net.
The Strategic Play for Intelligence Agencies
The disappearance of Mark Ruppert necessitates a shift in how the intelligence community handles personnel in emerging fields like UAP studies. The current model of "Muzzle and Monitor" is failing.
The immediate tactical requirement is the implementation of a specialized psychological support framework for individuals holding high-consequence anomalous data. This framework must operate outside the standard chain of command to ensure that seeking help does not result in the immediate revocation of security clearances, which is currently the primary deterrent for officials in distress.
Furthermore, the investigation into Ruppert must transition from a "Missing Persons" case to a "Counter-Intelligence Assessment." The priority must be determining whether his disappearance was a solo act of psychological preservation or if he was "assisted" by an entity interested in the data he carried.
The final strategic move for those tracking this case is to monitor the "digital exhaust" of known associates six to twelve months out. A "planned" disappearance often involves a pre-arranged contact point once the initial heat of the search subsides. If Ruppert is alive, his survival depends on the total integrity of his new perimeter; the first crack in that perimeter will likely be a financial or communicative attempt to reach back into his former life. Until then, his disappearance remains a successful execution of an evasion protocol designed by an expert in institutional surveillance.